Now Reading: Does a VPN Hide Your Location? Understanding VPN IP Address Masking, Privacy Limits & Government Detection
-
01
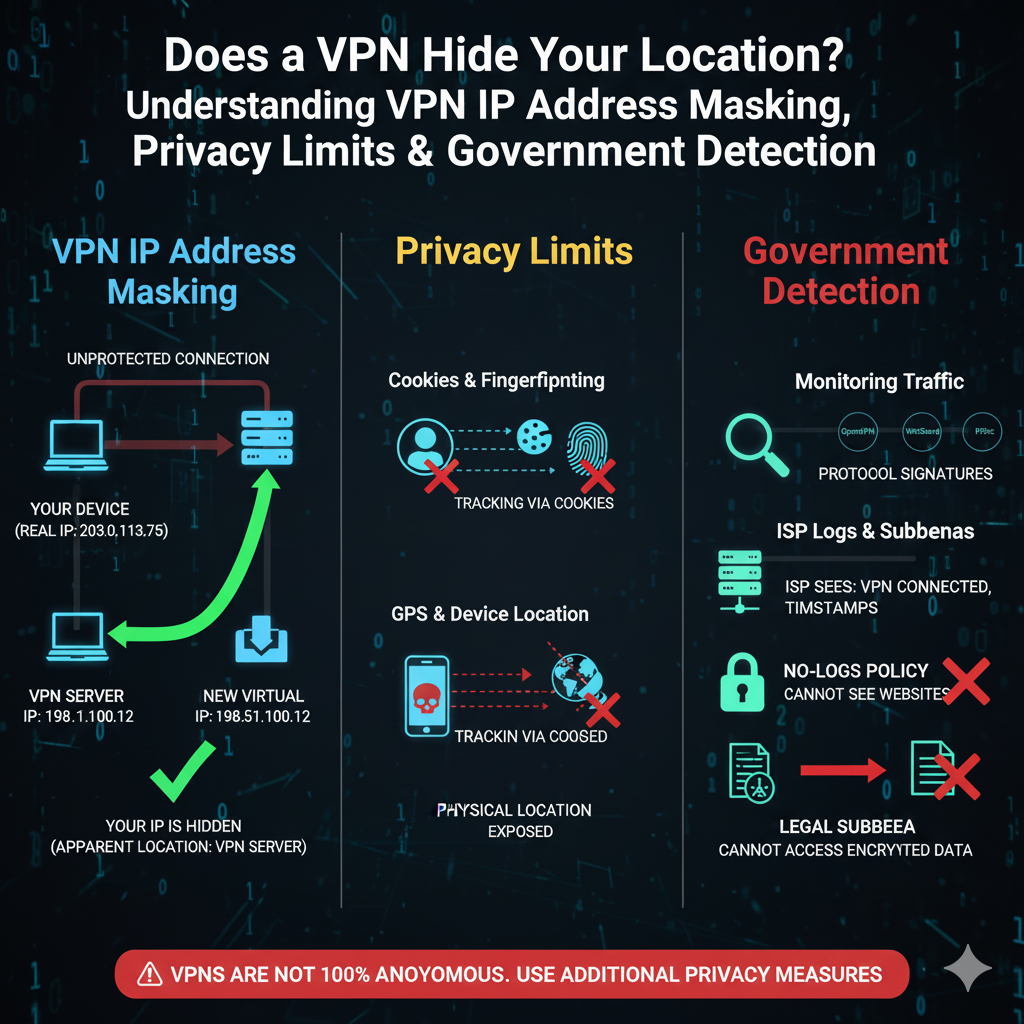
Does a VPN Hide Your Location? Understanding VPN IP Address Masking, Privacy Limits & Government Detection
Does a VPN Hide Your Location? Understanding VPN IP Address Masking, Privacy Limits & Government Detection
How VPNs Hide Your Location
Understanding IP Addresses and Location Tracking
An IP address is a unique string of numbers assigned by your Internet Service Provider (ISP) that identifies your device on the internet. Websites and online services use IP addresses to determine your approximate physical location, often down to your city or country. This enables location-based content, advertising, and sometimes even restrictions.
How VPNs Replace Your IP Address
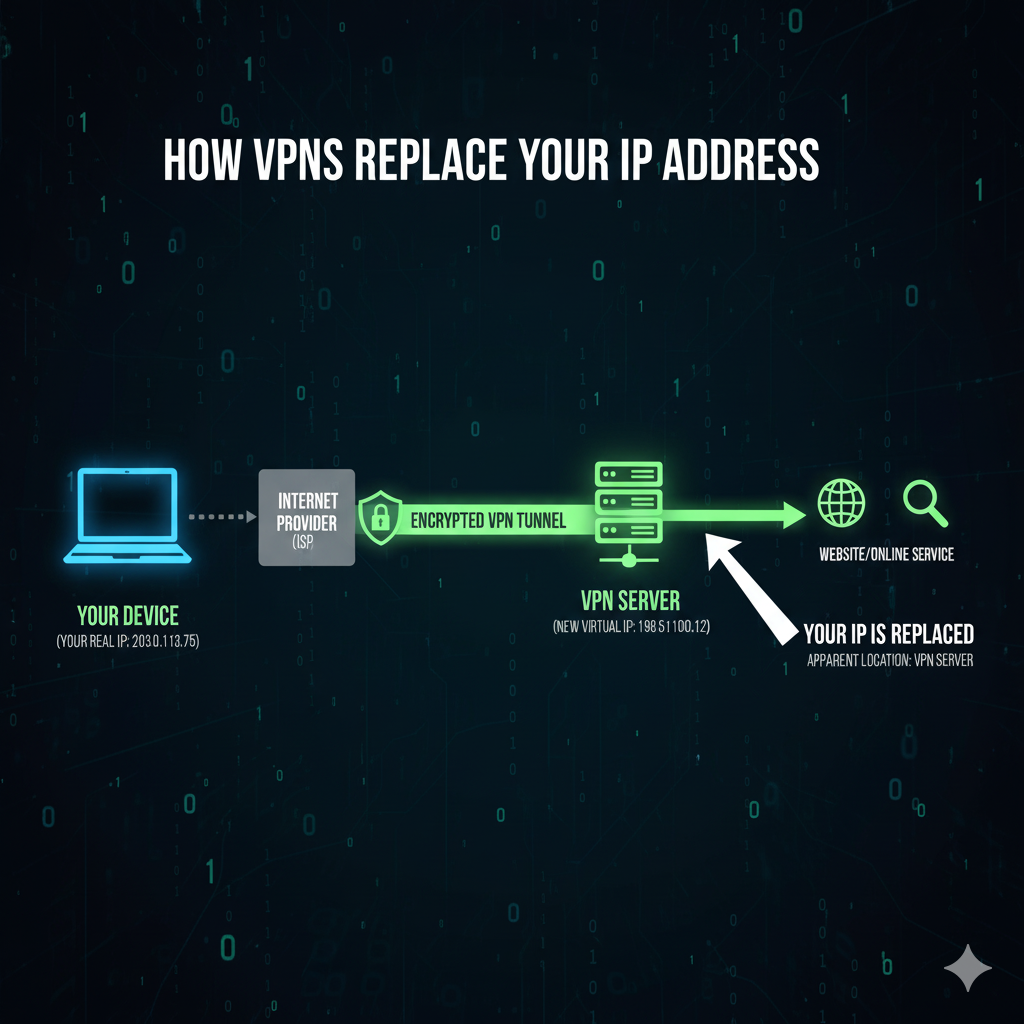
A VPN (Virtual Private Network) reroutes your internet traffic through a secure, encrypted tunnel to a server operated by the VPN provider. This process works as follows:
User → Encrypted Tunnel → VPN Server → Destination Website
During this routing, your original IP address is replaced with the IP address of the VPN server, effectively masking your real location. As a result, websites and ISPs cannot easily determine your true geographic location.
Location Spoofing via VPN Server Selection

VPNs allow users to choose servers in different countries, making it appear as though they are browsing from that location. This technique, called location spoofing, is commonly used for:
- Accessing geo-blocked content (e.g., streaming platforms, websites restricted by region)
- Maintaining online privacy and avoiding tracking
- Circumventing censorship or local network restrictions
By combining IP masking and server selection, VPNs provide a simple yet effective way to control what others can infer about your physical location online.
VPN Location Protection and Geo‑Restriction Bypass
How VPNs Bypass Geo‑Restrictions
Websites and streaming platforms often restrict content based on the user’s geographical location. This is done by detecting your IP address, which contains information about your country, region, or city. Platforms like Netflix, Hulu, Amazon Prime, and BBC iPlayer use this method to control what content is available in each region due to licensing agreements.
A VPN bypasses these geo‑restrictions by replacing your real IP address with an IP from another country. When you connect to a VPN server in the US, UK, Japan, or any other location, websites believe you’re physically located there. This tricks streaming services and geo‑locked platforms into giving you access to region-specific content.
Popular Use Cases
- Streaming foreign libraries: Access Netflix USA, Hulu, Disney+, or BBC iPlayer from anywhere.
- Unblocking censored websites: Especially useful in restrictive countries where services like YouTube, WhatsApp, or news websites may be blocked.
- Unlocking region‑locked apps and games: Get access to apps, game servers, and features not available in your region.
Limits of VPN Location Tracking and Privacy
Why VPNs Can’t Hide Device‑Specific Identifiers
Even though VPNs mask your IP address, they cannot hide hardware‑level and device‑specific identifiers, such as:
- GPS Location: If an app uses GPS (like Google Maps), it will still detect your actual physical location unless GPS spoofing is used.
- IMEI Number: Mobile carriers and device systems still know your IMEI, which VPNs cannot change.
- MAC Address: Local network hardware identifiers remain the same on Wi-Fi networks.
- SIM Information: Mobile network towers can still identify your approximate location.
- Browser Fingerprinting: Websites can detect device type, screen size, OS, browser version, fonts, plugins, time zone, and more — even with a VPN.
How Websites Track Users Despite Using a VPN
Even with your IP hidden, websites can still track or identify you using:
- Cookies & Local Storage: If you log in or previously visited the site, cookies can reveal your identity.
- Persistent Browser Fingerprinting: Sites combine dozens of device characteristics to create a unique fingerprint.
- Account Logins: Once you sign in (e.g., Google, Facebook, Netflix), your real identity becomes visible regardless of VPN use.
What Exactly Does a VPN Hide?
Summary of Protected Data
A VPN primarily protects the following:
- IP Address: Your real IP is masked, making it appear as though you’re browsing from the VPN server’s location.
- Location tied to IP: Websites and services cannot see your actual geographic location based on IP.
- Browsing activity from ISP: Your Internet Service Provider cannot monitor your online traffic.
- Public Wi-Fi activity from attackers: VPN encryption safeguards your data when using unsecured Wi-Fi networks.
What VPNs Don’t Hide
Despite the protection, VPNs have limitations and cannot hide:
- IMEI number: Your device’s unique identifier remains visible to mobile carriers.
- GPS-based actual device location: Apps using GPS can still detect your true physical location.
- Account activity on logged-in services: Your actions on services like Gmail, Netflix, or social media are visible once logged in.
- Device hardware identifiers: MAC addresses, system configurations, and other hardware-specific identifiers remain exposed.
VPN IP Address Leak Risks and Mitigations
What Is an IP Address Leak?
An IP leak occurs when your real IP address escapes the VPN’s encrypted tunnel, revealing your true identity or location. Common types include:
- DNS Leaks: Your DNS requests bypass the VPN, exposing your ISP’s IP.
- WebRTC Leaks: Browser features like WebRTC can reveal your IP even when connected to a VPN.
- IPv6 Leaks: VPNs without IPv6 support can accidentally expose your IPv6 address.
Leaks can compromise privacy, undermine geo-restriction bypassing, and expose your location to websites and hackers.
Tips to Prevent VPN Leaks
- Use a reliable VPN provider: Trusted providers actively prevent leaks and maintain strong encryption.
- Enable Kill Switch: Automatically disconnects your internet if the VPN drops.
- Disable IPv6 if unsupported: Prevents accidental exposure of IPv6 addresses.
- Keep apps and browsers updated: Ensures security vulnerabilities are patched.
- Use VPNs with built-in leak protection: Many premium VPNs include DNS and WebRTC leak safeguards.
How Governments Detect VPN Usage
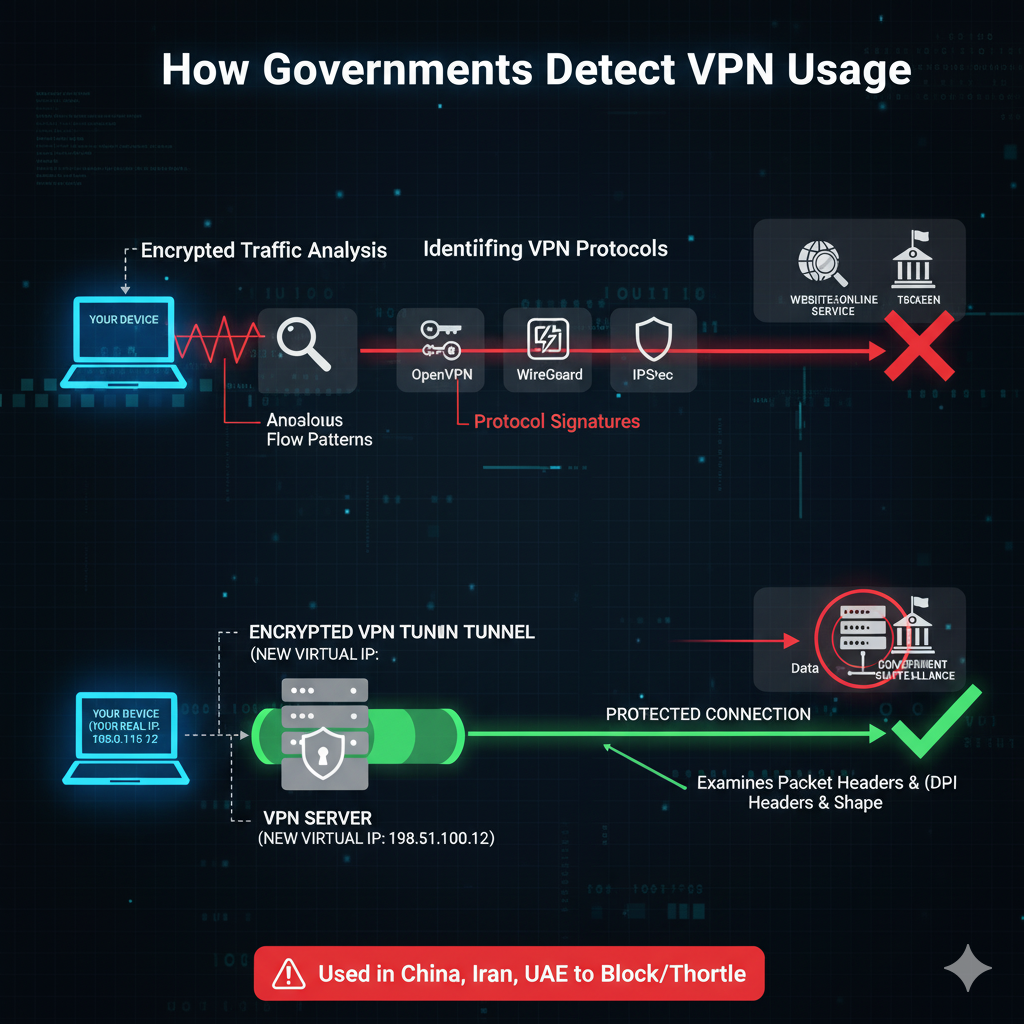
Monitoring Internet Traffic for VPN Patterns
Governments can identify VPN usage by analyzing internet traffic patterns:
- Encrypted traffic analysis: VPN data is encrypted, but its flow can look different from normal traffic.
- Identifying VPN protocols: Common VPN protocols like OpenVPN, WireGuard, and IPSec have distinct signatures.
- Deep Packet Inspection (DPI): DPI examines packet headers and shapes to detect VPN tunnels.
- Heavily used in countries like China, Iran, and the UAE to block or throttle VPN connections.
Recognizing Known VPN IP Addresses
Authorities maintain lists of VPN server IPs, making it easier to:
- Block access to these IPs entirely
- Throttle traffic from VPN servers to degrade performance
This is why some VPNs offer obfuscated servers that make VPN traffic look like regular internet traffic
What Information Governments Can Access
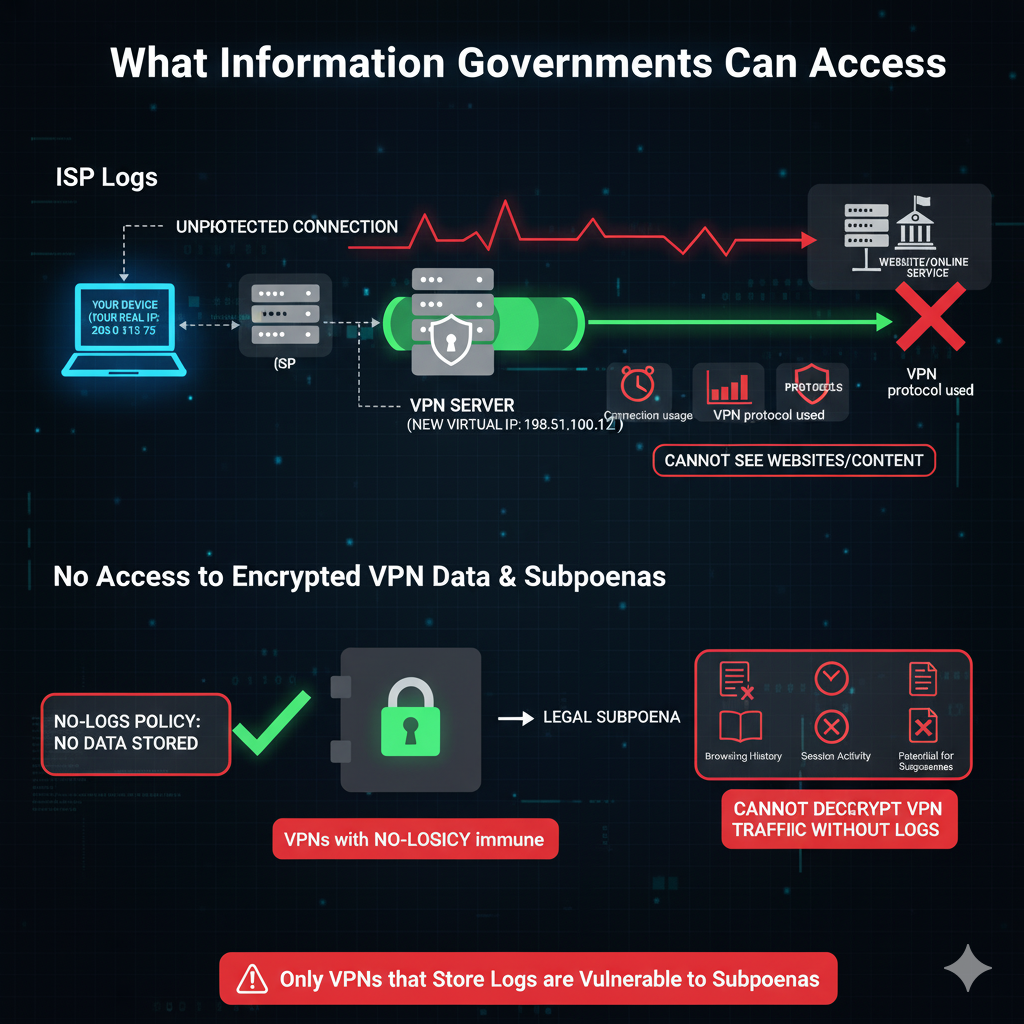
ISP Logs
Even when using a VPN, your Internet Service Provider (ISP) can see that you are connected to a VPN server. They can record:
- Connection timestamps
- Bandwidth usage
- VPN protocol used
However, they cannot see the actual websites you visit or content inside the encrypted tunnel.
No Access to Encrypted VPN Data
Without cooperation from the VPN provider, governments cannot decrypt VPN traffic. Only VPN providers storing logs could potentially reveal:
- Browsing history
- Session activity
Potential for Subpoenas
Law enforcement agencies may request VPN logs through legal subpoenas. This is only relevant for VPNs that store session or activity data. VPNs with a strict no-logs policy remain largely immune to such requests.
Government Measures to Block or Limit VPN Use
Blocking or Throttling VPN Servers
Governments often limit VPN usage by targeting the VPN servers themselves:
- Blacklisted server IPs: Known VPN IP addresses are blocked at the national or ISP level.
- Bandwidth throttling: During protests or political events, authorities reduce speeds for VPN‑related traffic to discourage use.
This makes many standard VPN servers slow or completely inaccessible.
Legal Enforcement in Restricted Countries
Some countries regulate or restrict VPN usage by law. Governments may:
- Impose fines and penalties for unauthorized VPN use
- Require VPNs to register with the state
- Monitor or prosecute VPN users depending on the severity
Examples: China, Russia, Iran, Oman, UAE, and others with strict digital surveillance policies.
Firewall & DPI‑Based Blocking
Countries with advanced censorship systems use:
- National firewalls to completely block VPN traffic
- Deep Packet Inspection (DPI) to detect and stop VPN protocols
- Blocking common protocols like OpenVPN or WireGuard
- Disrupting or degrading VPN connections so they become unusable
This makes regular VPN connections difficult or impossible without special configurations.
Techniques to Avoid VPN Detection
Obfuscated / Stealth VPN Protocols
Obfuscation hides VPN traffic by making it look like normal HTTPS:
- Masks VPN signatures
- Helps bypass DPI, firewalls, and region‑level restrictions
- Ideal for countries like China or Iran where standard VPNs are blocked
Many premium VPNs offer “stealth,” “obfuscated,” or “camouflage” modes for this purpose.
Multi‑Hop (Double VPN)
Multi-hop routes your connection through two VPN servers instead of one, boosting anonymity:
- Makes tracking more difficult
- Adds an extra layer of encryption
- Useful for high‑risk privacy tasks
Though slower, it provides stronger protection against surveillance.
Combining VPN With Tor
Using a VPN with Tor significantly increases anonymity:
- VPN → Tor hides Tor usage from your ISP
- Useful in high‑surveillance countries
- Prevents tracking by separating identity, IP, and browsing layers
Ideal for sensitive browsing where maximum privacy is required.
Limitations and Risks for Users
Free or Untrustworthy VPNs
Not all VPNs offer real privacy. Using free or unverified services can be risky:
- Logging user data: Some free VPNs store and sell browsing data to advertisers.
- Weak encryption: Inadequate encryption can make your traffic easy to intercept.
- Easily monitored or compromised: Vulnerable servers or poor security practices may expose your activities.
VPN IP Leak Risks
Even reliable VPNs can expose your identity if misconfigured or unsupported:
- Misconfiguration or unstable servers: Can result in accidental IP leaks.
- Browser-related leaks: WebRTC, DNS, or IPv6 leaks may reveal your true IP.
- Exposure to ISPs or websites: If leaks occur, your browsing activity can be traced despite using a VPN.
Importance of Choosing a Strong No-Logs VPN
To maximize privacy and security, select a VPN that offers:
- Audited no-log policies: Third-party audits ensure no user data is stored.
- Secure protocols: OpenVPN, WireGuard, or other strong encryption methods.
- Built-in leak protection and Kill Switch: Automatically blocks internet traffic if the VPN connection drops, preventing exposure.
FAQ Section
Q: Can the government track VPN users without the VPN provider’s logs?
- Governments can detect VPN usage, but cannot see your browsing activity without access to logs.
- Tracking your actual activity is only possible if the VPN keeps connection or session logs.
Q: Is using a stealth VPN always legal?
- Stealth VPNs are legal in most countries.
- In restrictive regimes, their use may be illegal, so users should always check local laws.
Q: What happens if my VPN provider logs my data?
- If logs exist, governments can access your browsing history via subpoena.
- Logging undermines the core purpose of privacy and anonymity.
Q: How to choose a VPN that minimizes detection risk?
- Look for stealth/obfuscation modes to bypass DPI and firewall blocks.
- Ensure the VPN has an audited no-logs policy.
- Use strong encryption and features like kill switch and leak protection.
Conclusion
- VPNs effectively mask your IP address and location, helping you access restricted content and protect online privacy.
- While they significantly improve privacy, they are not perfect—device identifiers, browser fingerprints, and account logins can still reveal identity.
- Governments can detect VPN usage but cannot see encrypted activity without cooperation or access to logs.
- For enhanced privacy, users should consider combining VPNs with Tor, secure browsers, and anti-tracking extensions.
- Choosing a trusted, no-logs VPN with leak protection is essential for true online anonymity.
















Pingback: Does a VPN Hide Your Location? Understanding VPN IP Address Masking and Anonymity - puretechzone.com